Items of № 8, 2017
DIGITAL UPGRADE OF THE GLOBAL ECONOMY: «EXPLOSION OF CONSTRUCTIVE DESTRUCTION»
V.K. Shultseva, Primakov National Research Institute of World Economy and International Relations RAS, senior researcher; vshul@imemo.ru
The main trends in the development of the ICT industry and vectors of its impact on the efficiency of economic entities under the conditions of creating a new complex model of the economy, less costly and more efficient, are considered. Particular attention is paid to the quantified assessment of the main signs of «digital maturity» of the OECD countries and the contribution of the digital component to the development of national economies.
Keywords: digitalization, technologies, innovations, economy, sharing, startups, «unicorns».
5G AND IoT NETWORKS AS INNOVATIVE ENVIRONMENT OF DIGITAL ECONOMY IN RUSSIA
V.O. Tikhvinskiy, MTUCI, professor, JSC NIITC, deputy CEO on innovation technologies, Dr.Sci.(Econ.); vtniir@mail.ru
The technological bases of the network infrastructure for the digital economy of Russia are considered. The features of the implementation of 5G-networks and Internet of things (IoT) are analyzed. The characteristics of these networks, technological and regulatory barriers to their implementation, business models of their use in industrial and consumer sectors of the digital economy are investigated. The prospects of implementing various radio access technologies in the implementation of 5G and IoT networks are considered.
Keywords: digital economy, Internet of Things (IoT) technologies,5G technologies, IMT-2020, business models for IoT, 3GPP, ITU.
SOFTWARE-HARDWARE COMPLEX FOR COMMUNICATION QUALITY TESTING ON THE BASIS OF ITU-T Q.3960 RECOMMENDATION
O.A. Gubskaya, Military Institute of Physical Culture, 1-st faculty, course officer-teacher; oksanochka23932393@mail.ru
E.A. Alisevich, Military Academy of Communications named after Marshal of Soviet Union S.M. Budjonny, department Technical support of communication and automation, associate professor; Ph.D; ezhilkina@yandex.ru
V.A. Kulik, SPbSUT, department Communication Networks and Data Transmission, assistant; vaklicr@gmail.com
R.V. Kirichek, SPbSUT, department Communication Networks and Data Transmission, associate professor, Ph.D.; kirichek@sut.ru
A.S. Borodin, PJSC Rostelecom, representative member in Geneva, Ph.D; aleksey.borodin@rt.ru
Testing methods of uplink, downlink throughput and RTT latency between two devices, functioning on the «last mile» level of carrier network using different network protocols (HTTP/HTTPS, MQTT, XMPP, AMQP, WebSocket, CoAP, QUIC and others) were analyzed. Based on the Recommendation ITU-T Q.3960 architecture of software-hardware complex for testing the quality of service, method for testing network parameters between the last mile device and remote cloud service as well as between end nodes of local network, supporting the function of network address translation (NAT), were developed. The data transmission protocol for the software-hardware complex was described.
Keywords: telecommunication, testing, e2e, uplink, downlink, latency, QoS, HTTP, STUN, NAT.
DEVELOPMENT OF THE NETWORK CAPACITY MODEL USING THE MiMa-ALGORITHM
T.D. Tashev, Researcher Institute of Information Technologies at the Bulgarian Academy of Sciences, research scientist; ttashev@iit.bas.bg
A.S. Bakanov, Researcher Department of Engineering Psychology and Ergonomics Institute of Psychology RAS, research scientist, Ph.D; arsb2000@pochta.ru
The article is devoted to the issues connected with the development of the network capacity model using the MiMa-algorithm. Within the framework of researches the model of network capacity was developed, the obtained results are described.
Keywords: information systems, network capacity model, MiMa-algorithm.
MODELS AND METHODS OF OPERATIONAL MANAGEMENT OF TELECOMMUNICATION NETWORKS
A.B. Goldstein, SPbSUT, associate professor, Ph.D; agold@niits.ru
Instead of traditional OSS/BSS approach, a new telecommunication network management model, that meets the requirements of NGN/IMS- and post-NGN/ IMS-networks, is proposed.
Keywords: OSS/BSS, business intelligence, post-NGN, IP/MPLS, multi-agent systems, queuing theory, network management.
UNLICENSED SPECTRUM LTE NETWORKS
V.G. Skrynnikov, PJSC MTS, expert, Ph.D; vskrynnikov@list.ru
Issues connected with the use of unlicensed spectrum in mobile LTE networks are systematized: what is the unlicensed spectrum for LTE; its features in Europe and Russia; standardization of LTE technology for unlicensed spectrum; mechanisms of its use in LTE and features of technical solutions using an unlicensed spectrum.
Keywords: unlicensed spectrum, carrier aggregation, Wi-Fi, LTE-U (LTE-Unlicensed), LAA-LTE (Licensed-Assisted-Access–LTE), LWA(LTE-WLAN), DFS (Dynamic Frequency Selection), LBT (Listen-Before-Talk).
ALGORITHM FOR OPTIMAL DECODING OF NONBINARY EQUIDISTANT CYCLIC CODES
V.V. Zelenevskiy, Military Academy RVSN named after Peter the Great (Serpukhov branch), professor, Dr.Sci.(Tech.); Zelenevsky.Vladimir@gmail.com
Yu.V. Zelenevskiy, military unit 33965, associate professor, Dr.Sci.(Tech.); sys1434@mail.ru
A.V. Zelenevskiy, CJSC Firma STC KAMI, leading expert, Ph.D; dieselmail@inbox.ru
A.S. Durnov, military unit 33965, researcher; tema070@mail.ru
The new algorithm for optimal decoding of non-binary equidistant cyclic codes based on algebraic analysis of accepted code combination in finite Galois fields is proposed. The algorithm allows to refuse complete enumeration of enabled code combinations in the analysis of the accepted combination, as well as to reduce the decoding time and increase the packet length of the errors corrected by the decoder. By means of simulation modeling numerical estimates of the specified advantages depending on length of the corrected error burst and decoding time are obtained.
Keywords: primitive element of the Galois field, primitive polynomial, equidistant non-binary code, optimal decoding, probabilitiesof erroneous decoding of non-binary code word and message bits.
PERMUTATION DECODING AS A TOOL TO IMPROVE THE ENERGY EFFICIENCY OF DATA EXCHANGE SYSTEMS
A.A. Gladkikh, Ulyanovsk state technical university, professor, Dr.Sci.(Tech.); a_gladkikh@ mail.ru
On the basis of estimates of the asymptotic efficiency of the various redundant block code processing schemes, the rationale for the development of means of permutation decoding of these codes is given. It is proved that the cognitive procedure is promising for construction of such decoders. It allows significantly reduce the complexity of decoder processor implementation. For the first time the regular methods of fast matrix transformations of generating matrices of rearranged codes are considered, which make it possible to exclude from the decoding algorithm the procedures of searching of rearranged code matrix determinant and analog of this matrix in a systematic form. On the basis of analytical modeling, the energy gain of the code at application of permutation decoding with respect to well-known binary codes decoding schemes is estimated.
Keywords: soft symbol solution, permutation decoding, decoder cognitive map, concatenated coding.
ALGORITHM OF FUNCTIONING OF THE EDUCATIONAL LABORATORY STAND OF A PROTECTED DATA NETWORK ON THE BASIS OF VIRTUAL CHANNELS WITH HIGH REQUIREMENTS TO QUALITY OF SERVICE
V.A. Matveev, Bauman University (BMSTU), head of scientific-technical complex facility of informatics and control systems, professor, Dr.Sci. (Tech.); v.a.matveev@bmstu.ru
M.A. Basarab, BMSTU, head of department of information security, professor, Dr.Sci. (Phys.-Math.); bmic@mail.ru
R.A. Belfer, BMSTU, department of information security, associate professor, Ph.D.; a.belfer@yandex.ru
A.V. Kravtsov, Scientific Research Institute of Scientific Research (Moscow) Central Research Institute of the Air Forces, senior researcher, skyak78@gmail.com
D.I. Merzlyakov, BMSTU, student; merzdan@gmail.com
Features of data transmission networks belonging to the category of special purpose communication networks are considered. A brief description of the algorithms for establishing connection, transmitting data and resetting a connection based on virtual channels are given on the example of a hypothetical network structure with a bundle of several routes. These algorithms provide implementation of requirements for safety, reliability, delay and probability of message delivery.
Keywords: data networks, information security, reliability, delay,probability of message delivery.
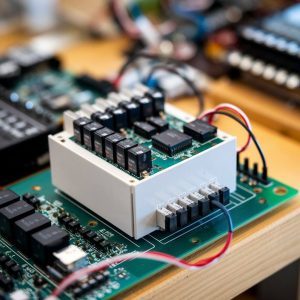
COMPARISON OF CHARACTERISTICS OF PHASE CONTROLLED BRIDGE RESONANT DC/DC-CONVERTERS
B.A. Glebov, Moscow Power Engineering Institute (National Research University), associate professor, Ph.D.; glebovba@mail.ru
V.A. Zhigachev, Moscow Power Engineering Institute (National Research University), postgraduate student; usual.one@gmail.com
Based on the simulation results the main characteristics of several versions of bridge circuits of resonant DC/DC-converters using power transistors phase control principle are compared. Keywords: bridge resonant converter, phase shift control, ZVS, topology comparison.