Items of № 12, 2021
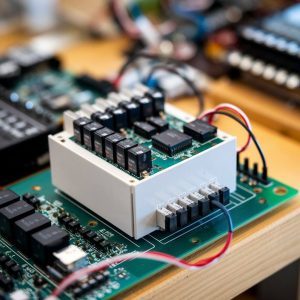
ROUTE SELECTION METHOD FOR HIGH-DENSITY WIRELESS IOT NETWORK
- S.N. Bushelenkov, PJSC Rostelecom, North-West macro-regional branch, access network planning department, chief specialist; bsn1980@yandex.ru
- A.I. Paramonov, The Bonch-Bruevich Saint-Petersburg State University of Telecommunications, department of communication networks and data transmission, professor, Dr.Sci.(Tech.); alex-in-spb@yandex.ru
Keywords: Internet of Things, IoT, high-density network, route, data transfer rate, delay, optimization
The article presents the results of the study of the dependence of the data transfer rate on the route parameters in wireless Internet of Things (IoT) networks. A method for choosing the number and positions of nodes for organizing a route in the IoT network is proposed. The method takes into account the influence of the distance between the nodes of the route and their number on the delay in data delivery and the speed of data transmission along the route. The method allows one to obtain a gain in the attainable data transfer rate in comparison with methods of choosing a route based on the criterion of the number of transit nodes.
IDENTIFICATION OF LONG-RANGE NARROWBAND WIRELESS NETWORK DEVICES BASED ON DIGITAL OBJECT ARCHITECTURE USING BLOCKCHAIN TECHNOLOG
- A.V. Pomogalova, The Bonch-Bruevich Saint-Petersburg State University of Telecommunications (SPbSUT), department of software engineering and computer engineering, assistance lecturer; a.l.b.i.n.a@bk.ru zaharov.spbgut@gmail.com
- D.D. Sazonov, SPbSUT, department of software engineering and computer engineering, postgraduate; dim-saz@yandex.ru
- A.S. Borodin, representative of PJSC Rostelecom in the ITU, Ph.D., aleksey.borodin@rt.ru
- R.V. Kirichek, SPbSUT, head of the department of software engineering and computer engineering, associate professor, Dr.Sci.(Tech.); kirichek@sut.ru
Keywords: blockchain, DOA, smart contract, identification, digital object architecture, Internet of Things, IoT.
The article is devoted to the study of the possibility of interaction of the system of identification of devices of the Internet of Things (IoT) with the private instance of blockchain network on the basis of the open-source client to optimize the operation of the identification system. The issues of blockchain network organization and the architecture of the developed model stand are considered, a number of studies have been carried out. The results of interaction of the identification system with the blockchain network in the identification and recording device in the blockchain network, as well as the response time of the blockchain network when requesting data for checking or confirming the issued identifiers are presented. The work of the blockchain network was analyzed as a tool for login of all changes in the identification system to prevent falsification and substitution of the identification data of devices and IoT sensors.
USING FEDERATED MACHINE LEARNING FOR ACCESS POINT SELECTION IN THE HETEROGENEOUS NETWORK
- R.Ya. Pirmagomedov, Tampere University, researcher, Ph.D.; rustam.pirmagomedov@tuni.fi
Keywords: IMT-2020, IMT-2030, machine learning, heterogeneous networks, mobile networks.
The problem of selecting a wireless access network in a highly heterogeneous environment has been analyzed and solved. A network selection model based on the analysis of a wireless network environment using a federated reinforcement machine learning system is proposed. A model has been developed to estimate the theoretical average capacity available to the user in a highly heterogenic access network. The effectiveness of the proposed method was evaluated using a series of experiments. The article is concluded with a discussion regarding the applicability of the proposed method for IMT-2020 and IMT-2030 networks.
TELECOMMUNICATIONS ENVIRONMENT AND PROBLEMS OF DIGITAL FOOTPRINT DATA OF SUBJECTS OF DIGITAL SOCIETY
- S.V. Kizima, FSUE NIIR, Research center of big data processing systems, director, ITU expert, Dr.Sci.(Tech.); StanislavKizima@mail.ru
- F.V. Kidalov, SFI Information and Analytical Center for Healthcare, deputy director general; kidalovfv@mos.ru
- D.A. Paltsyn, FSUE NIIR, director of the Access network research center; Palcin@niir.ru
Keywords: digital society, telecommunications infrastructure, network service systems, digital footprint, big data, data storage and processing systems, ethics and practice of personal data storage and processing.
The article deals with big data problematic, approaches to the organization of storage, use, and data security of digital footprint of subjects-users of digital network service systems. Principles and methods of storage of big data and problems of realization of users’ rights to their «digital footprint» in the telecommunications environment of network service systems are considered. The article is debatable and calls for a joint search for the optimal and effective use of digital footprint data for the benefit of every citizen as well as the digital society as a whole.
ESTIMATION OF THE MESSAGE TRANSMISSION PROBABILITY IN CHANNELS WITH ERRORS PACKETS
- M.L. Maslakov, JSC Russian Institute for Power Radioengineering, leading research fellow, Saint-Petersburg State University of Aerospace Instrumentation, head of a department, Ph.D.; maslakovml@gmail.com
- S.A. Kudryashova, The Bonch-Bruevich Saint Petersburg State University of Telecommunications, student; kukuruza290101@mail.ru
Keywords: convolutional codes, interleaver, error packet, bit error rate, message error rate.
The paper deals with the transmission of messages over channels with error packets. A model of a discrete channel has been designed with the formation of both single errors and packets of errors with a given probability. The model provides estimates of the message error rate for various conditions. The results of the numerical simulation are presented.
A METHOD FOR DETECTING ANOMALIES IN NETWORK COMPUTER TRAFFIC USING THE LSTM NEURAL NETWORK
- A.M. Kribel, S.M. Budyonny’s Military Academy of Communications (MAC), adjunct; nemo4ka74@gmail.com
- O.S. Lauta, The Admiral Makarov State University of Maritime and Inland Shipping, professor, Dr.Sci.(Tech.); Laos-82@ya.ru
- A.V. Filin, S.M. Budyonny’s MAC, applicant; kadet58v@yandex.ru
- A.S. Fen, FSUE NIIR, Access Network Research Center, head of a department; Fen@niir.ru
Keywords: computer network, anomaly detection, cyberattack, web application firewall, neural network, LSTM, autoencoder.
The possibilities of using artificial neural networks of complex architecture (in particular, based on Long Short-Term Memory (LSTM)) are investigated to detect network anomalies caused by cyber attacks aimed at bypassing vulnerabilities of web application firewalls (Web Application Firewall, WAF), which are very difficult to detect by other means. It is proposed to use the LSTM capabilities simultaneously with the autoencoder. The issues of software implementation of this approach are considered. Experimental results based on the generated dataset confirmed the high efficiency of the development: the technique allows detecting cyberattacks in real or near real time.
INFORMATION AND TELECOMMUNICATION NETWORK SECURITY MANAGEMENT METHODOLOGY
- M.A. Karpov, S.M. Budyonny’s Military Academy of Communications (MAC), adjunct; karpuh.djan@mail.ru
- M.V. Mitrofanov, S.M. Budyonny’s MAC, head of the department of security of special-purpose infotelecommunication systems, Ph.D.; vonafortim@yandex.ru
- O.S. Lauta, The Admiral Makarov State University of Maritime and Inland Shipping, professor, Dr.Sci.(Tech.); laos-82@yandex.ru
- D.A. Paltsin, FSUE NIIR, Access Network Research Center, director; Palcin@niir.ru
Keywords: information and telecommunication network, script forecast, management system, situational management, ITCN security system.
The issues of situational management of complex dynamic systems are investigated. Relevant works in the field of situational management of protection systems are analyzed. The article presents the results of the development of an efficient control algorithm that allows reducing the state space of the controlled object. The presented technique makes it possible to predict the number of control iterations depending on the segment of the state space and the selected number of transitions. This approach allows you to act on complex dynamic systems in real time, while the cost of the computing power of the control system and its subsystems is reduced.
CASSEGRAIN TYPE DUAL-REFLECTOR ANTENNA CALCULATION METHOD
- A.M. Somov, FSUE NIIR, expert, professor, Dr.Sci.(Tech.); somov-am@list.ru
- R.V. Kabetov, Moscow Technical University of Communications and Informatics, associate professor, Ph.D.; kabetov_rv@mail.ru
Keywords: reflector antenna, Cassegrain two-reflector antenna, aperture method, noise temperature.
A method for calculating a two-reflector Cassegrain antenna is proposed, characterized by the introduction of a virtual additional irradiator to increase the accuracy of calculations of directional properties and noise temperature. An example of the antenna calculation is given.